In the last couple of weeks, I’ve started getting this error ~1/5 times when I try to open one of my own locally hosted services.
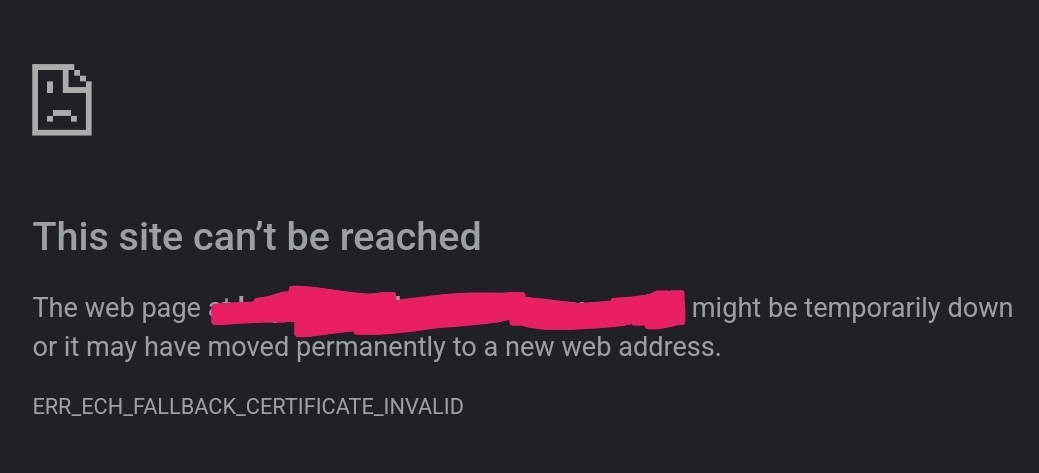
I’ve never used ECH, and have always explicitly restricted nginx to TLS1.2 which doesn’t support it. Why am I suddenly getting this, why is it randomly erroring, then working just fine again 2min later, and how can I prevent it altogether? Is anyone else experiencing this?
I’m primarily noticing it with Ombi. I’m also mainly using Chrome Android for this. But, checking just now; DuckDuckGo loads the page just fine everytime, and Firefox is flat out refusing to load it at all.
 Firefox refuses to show the cert it claims is invalid, and ‘accept and continue’ just re-loads this error page. Chrome will show the cert; and it’s the correct, valid cert from LE.
Firefox refuses to show the cert it claims is invalid, and ‘accept and continue’ just re-loads this error page. Chrome will show the cert; and it’s the correct, valid cert from LE.
There’s 20+ services going through the same nginx proxy, all using the same wildcard cert and identical ssl configurations; but Ombi is the only one suddenly giving me this issue regularly.
The vast majority of my services are accessed via lan/vpn; I don’t need or want ECH, though I’d like to keep a basic https setup at least.
Solution: replace local A/AAAA records with a CNAME record pointing to a local only domain with its own local A/AAAA records. See below comments for clarification.


I’ve fixed the same issue for me.
Originally I had this in my Local DNS settings in my Pi-Hole:
- service1.domain 10.0.0.4 - service2.domain 10.0.0.4 - service3.domain 10.0.0.5I changed that to this:
- host1.domain 10.0.0.4 - host2.domain 10.0.0.4And then I added CNAME Records to the services like this:
- service1.domain host1.domain - service2.domain host1.domain - service3.domain host2.domainThis fixed the whole thing for me :)
Edit: Gonna add some more info
The trick that makes this work, and probably will for you too, and allow you to keep your HTTPS queries, is that Pi Hole will just not ask upstream, if it has the DNS name in the CNAME records. Those CNAME records will have to point to a domain, that Cloudflare doesn’t know about. That way there is no other records upstream that will confuse the DNS server and your browser.
The hostname you have in your local DNS records that your CNAME points to, will be something only known locally for you.
@bobslaede@feddit.dk I could kiss you. You’ve been invaluable my friend, thank you!
Just gave this a test: CNAME ombi.domain -> local.domain with cloudflares proxy re-enabled.
Now the HTTPS, A, and AAAA requests all receive the CNAME response and browsers are happy. I didn’t even have to modify ngnix to recognize local.domain like I thought I might.
Awesome! I’m glad that it worked. It took me a while to figure out, when it happened to me. Glad that I could make your life easier :)