+-----------------+
| . local server |
+-.---------------+
< . >
< . >
< . >
< . >
< . >
+-.-----------------------+
| . serveo/localhost.run |
+-.-----------------------+
< . >
< . > +----------------------+
< . > | . raw data |
< . > | < . > encrypted data |
< . > +----------------------+
+-.----------+
| . clients |
+------------+
hellow,
i wanna host things (nextcloud, bin, syncthing) myself but im under cg nat so i cant do it the regular way. i have to tunnel my way out. the only concern is that, the raw data is readable by the ssh server (ie. serveo/localhost.run), but i dont anyone elses eyes on my data
sorry for my broken english.
edit:
- syncthing (solved): https://docs.syncthing.net/users/untrusted.html
- bin (solved): https://github.com/HemmeligOrg/Hemmelig.app?tab=readme-ov-file#features
- nextcloud: ???
please clarify me.
if i setup a vpn which provides encryption on my local server, can i go like this
+------------------+
| . local server |
+-< . >------------+
<< . >>
<< . >>
<< . >>
<< . >>
<< . >>
+-< . >----------------------+
| < . > serveo/localhost.run |
+-< . >----------------------+
<< . >>
<< . >> +-------------------------------------+
<< . >> | . raw data |
<< . >> | < . > vpn encrypted data |
<< . >> | << . >> vpn encrypted data over tls |
<< . >> +-------------------------------------+
+-< . >-------+
| . clients |
+-------------+
sorry i dont know how to express this in words
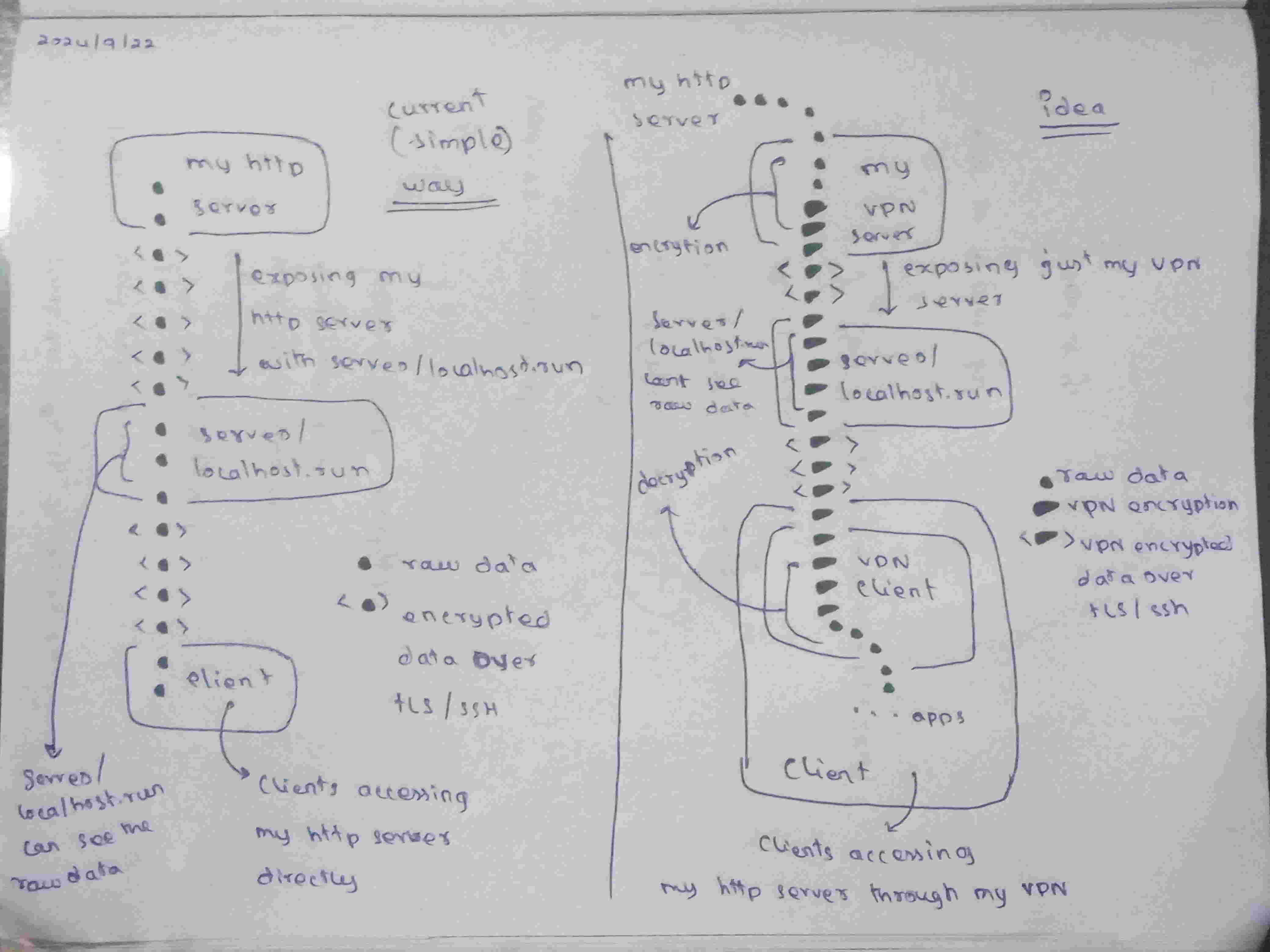
this is what i was trying to say. so the idea, is that okay?
I personally rent the cheapest VPS I could find and put Tailscale on it. My server at home then connects to that Tailscale network and the VPS runs nginx acting as a proxy forwarding everything to the server through Tailscale.
Besides having no annoying networking issues it also has the benefit that I can move houses without having to update A records to have the domain point to the new IP address because the VPS IP ofc remains the same.
Another (and to some degree more flexible AND simpler) solution is rathole: still requires you to host it somewhere, but it’s got a little more flexibility.
Edit: I’m not a fan of VPN tunnels in general, because for most people all you’ve done is made a remote server that, if it’s compromised, will have unfettered and complete access to your internal network via the VPN tunnel.
There are ways to mitigate that but, for what I suspect is the majority of people asking about how to do this, they’re outside of a reasonable technical ask.
(Rathole works similar to an argo tunnel, in that it initiates a connection to the VPS, and then passes traffic limited to a specific port or application back and forth, rather than being a nice open tunnel.
wait. please clarify me.
if i setup a vpn which provides encryption on my local server, can i go like this
+------------------+ | . local server | +-< . >------------+ << . >> << . >> << . >> << . >> << . >> +-< . >----------------------+ | < . > serveo/localhost.run | +-< . >----------------------+ << . >> << . >> +-------------------------------------+ << . >> | . raw data | << . >> | < . > vpn encrypted data | << . >> | << . >> vpn encrypted data over tls | << . >> +-------------------------------------+ +-< . >-------+ | . clients | +-------------+sorry i dont know how to express this in words
Yes
That ASCII art breaks on mobile devices :/
It’s mostly fine on my phone, just go landscape to see the broken bit
Looks fine for me using the web interface
The short answer is: you can’t do this.
The long answer is: you need to go through the process of getting a server you own and have provisioned installed at some colocation/datacenter place. It will be expensive to buy the server, expensive to buy rack space, and you will need to go through significant background and security checks in order to be allowed by the company to do this.
If that sounds terrible, and it is, you can use an overlay network like nebula. It still requires that you have a “server” somewhere, but you can use a $10/yr vps to host that. Your “server” is, in nebula’s terminology, the “lighthouse” node. All it does is punch through nats so people who connect to your overlay vpn are able to see each other.
Your vps provider can still see your data on the lighthouse though, so don’t keep your root certificate on it and use unique credentials. Traffic doesn’t flow through the lighthouse, so you don’t need to worry about snooping, but it’s possible for the vps provider to add themselves to the trusted certificate and get on your vpn. So you have to have good security on your internal network.
thanks for both answers. the second option, one i cant afford.
i did some research, the first the answer is partilly correct ig. for example syncthing offers password protection (https://docs.syncthing.net/users/untrusted.html) and for the bin, it provides client side encryption (https://github.com/HemmeligOrg/Hemmelig.app?tab=readme-ov-file#features) which will protect me even over plain http connection ig. please correct me if im wrong
these are product specific feature, so generally, as you said, no is the answer ig. i wish nextcloud offers something like. thanks again
I just saw your second diagram. If all you’re worried about is serveo being able to see, you could do all your http server stuff with https and require ECH on the client side and you’d be okay?
I’m not 100% that would work perfectly, especially if DNS is involved, but I don’t think serveo messes with DNS.