Cups only listens on local host only by default. Also it requires you to connect to a printer which is unaffected by the Firewall.
Possibly linux
I know nothing!
- 571 Posts
- 8.83K Comments
So some obscure thing you experienced 10 years ago is now the standard? I have been doing this a while and what you are describing is Franky crazy and I’ve never scene it outside of some business plans with bring your own device.

 41·11 hours ago
41·11 hours agoThat’s why I posted it. It has been rolled
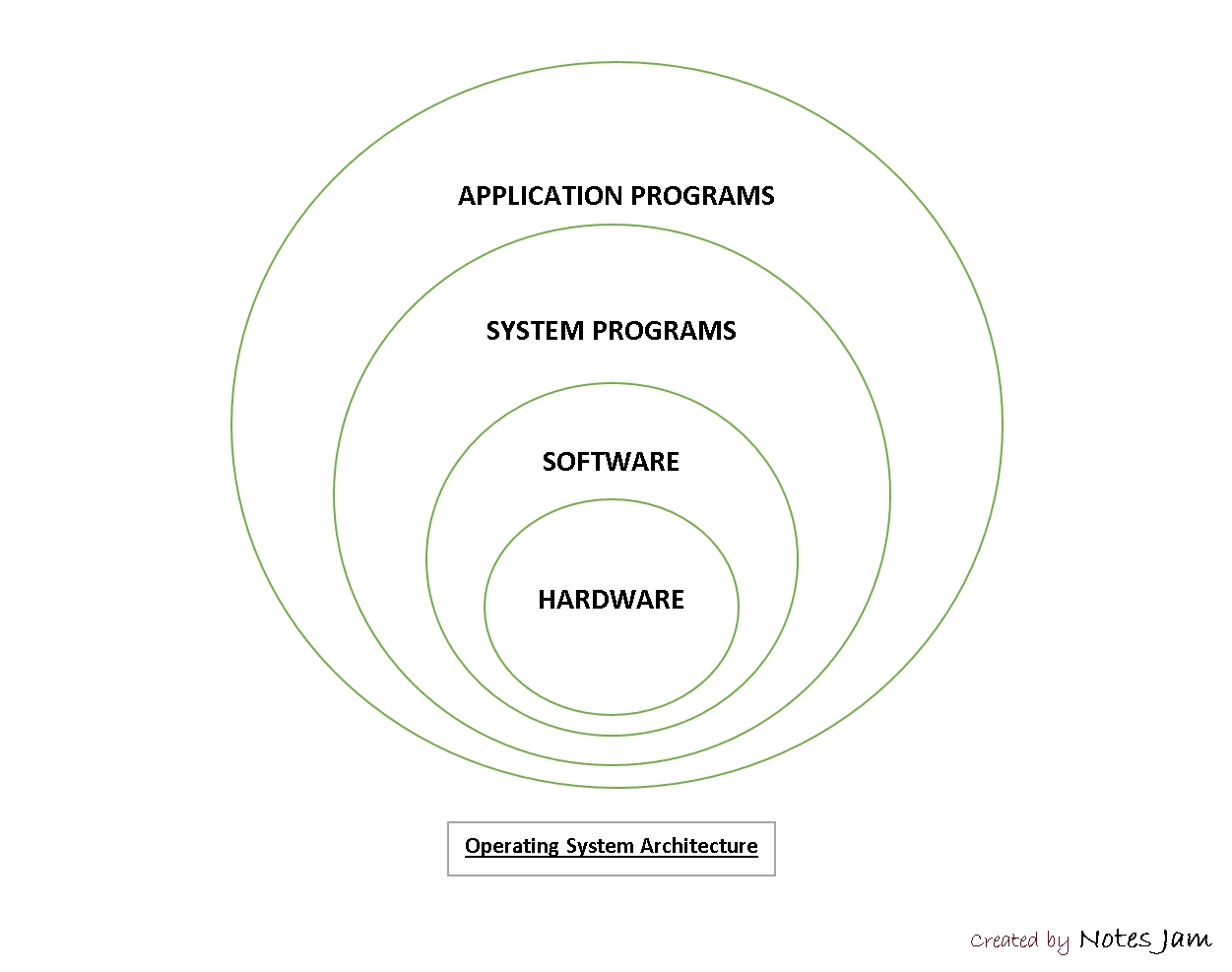
Computers are built on abstraction. You start at the most abstracted layer and work your way down. I would next check what resolutions are exposed in the kernel. If 5k isn’t exposed I would check the kernel itself. At the very bottom is hardware but I think this is a software issue. It may just be flat out not supported by Linux.
You know enough to be dangerous…
Why would an ISP assign a public IP to a users device? That wouldn’t make any sense. IPs are rare and expensive so that wouldn’t waste it on you. Each customer gets one IP and that is shared for all devices via NAT.
What your describing doesn’t make any sense

 21·16 hours ago
21·16 hours agoWhat else would you want?
You don’t understand local host. Services listen on 127.0.0.1 which is a local only address. You can only connect to it locally
I would advise that you ignore a lot if the advise here and do your own research. You probably don’t need a local Firewall and if you want to block content use DNS and browser extensions
This is good sane advise. I think a lot of people here don’t understand networking
Please stop giving bad advise. The local firewall is not the same as the public firewall and nat on the router. Your comment is incredibly misleading. You can have no Firewall and the services will not be available publicly
No one uses IPtables as a Firewall. That would be insane. Instead you set Firewall rules which then translate to IPtables under the hood
I’m not sure how Wireshark is related to firewalls honestly. It is mostly a layer 1 and 2 tool
Why are we recommending Wireshark? That doesn’t make any sense what so ever. If anything have them run a port scan with nmap.
This is crazy advise
You don’t understand networking. The local firewall will only stop traffic coming in locally and your average Linux desktop doesn’t have services listening outside of localhost anyway
Not unless it is a server distro
Not really
This is not great advise to say the least. You want to block all incoming but allow all outgoing.
Also visiting a https site will not magically ports. It uses 443/tcp and if you are using a site with WebRTC (used for calls on platforms like teams) ports 443/UDP and 50000-65535/UDP. However, there is no reason you need to know that unless you are in a professional field
Its good practice to have a firewall local as well. However, you are right it about it not being to critical
In that case I think it might be at a lower level.
















They poked the bear and now they are getting mauled. They should of just focused on the Way back machine